
Let’s face it—cloud security isn’t just a checkbox anymore. In today’s remote-first, hybrid, everyone’s-logging-in-from-somewhere world, keeping your Azure environment locked down is absolutely critical. On-premise environments at least had the illusion of protection via perimeter firewalls and network boundaries. But once you move into the cloud? That perimeter goes poof. Your data, your apps, and your users are potentially reachable from just about anywhere—including devices and accounts you might not even control.
And let’s be real: Azure gives you an incredible toolbox for securing your environment—but that toolbox is deep. Knowing where to start can feel a bit like being handed a spaceship and told to “just fly it.”
That’s why Conditional Access is such a great place to begin.
Conditional Access (CA) is one of the most powerful, flexible, and frankly, underrated tools Microsoft gives you to control how users access your data. It’s your digital bouncer, your velvet rope, your custom security checkpoint that adapts to who is trying to do what, from where, and on what kind of device. If you’re looking to lay a foundation for solid, scalable cloud security, this is where your journey begins.
In this post, I’ll walk you through not just what Conditional Access is—but why it matters, how to implement it effectively, and how it fits into your broader Azure security game plan. Whether you’re just getting started or brushing up, my goal is to make this feel more like a guided tour than a technical whitepaper.
Ready to dive in? Let’s do this.
What is Conditional Access?

Think of Conditional Access as your custom-built security checkpoint inside Azure. It lets you set the rules for who gets through the door, under what conditions, and whether they’re allowed to sit in the lobby or head straight into the server room.
At its core, Conditional Access policies are your gatekeepers. They control access to your cloud resources based on a combination of signals—who the user is, what device they’re on, where they’re coming from, and what they’re trying to access. You get to define what “safe” looks like, and then enforce that standard automatically.
Let’s say you have a user trying to get into a SharePoint site. A basic policy might say: “Sure, you can come in—but only after you’ve passed MFA.” Easy. But now imagine that same user is trying to access your Finance team’s SharePoint—sensitive stuff, payroll, budget projections, maybe some compliance-relevant data. That’s a different ballgame. You could require not just MFA, but also that they’re using a compliant, corporate-managed device and not some random laptop from their cousin’s garage.
And that’s where Conditional Access really shines—it lets you apply context-aware, granular security without creating chaos for your users (or yourself).
Microsoft’s Zero Trust model underpins a lot of this. In short: never trust, always verify. Identity, device posture, location, app sensitivity—all of it plays into whether access is granted or denied. With Conditional Access, you can build policies that enforce things like:
- Requiring MFA for all users
- Blocking legacy authentication (those old protocols are trouble)
- Restricting access based on device compliance, as defined in Intune
- Triggering extra steps if a device or sign-in is marked “risky” by Defender for Endpoint
You can start simple and scale up. And the best part? These policies run quietly in the background—when done right, users hardly notice. But you’ve just raised your security posture in a big way.
Why Conditional Access is Important
Let’s be honest—Azure doesn’t come out of the box with all the walls and doors you’d expect in a secure environment. When you spin up a new tenant, it’s like getting the keys to a wide-open floor plan. Sure, everything’s clean and new, but there’s nothing stopping people from wandering wherever they want unless you start putting up some boundaries.
That’s where Conditional Access comes in.
Think of your Azure tenant like a big office building. Conditional Access is how you build out the rooms, install security doors, assign keycards, and decide who can enter the break room versus who can get into the executive suite. It lets you reduce your attack surface by controlling not just who can access what—but also how and under what circumstances.
Let’s say someone logs in from a known device in your corporate office—great! Low risk. But if that same account tries to connect at 3 AM from a hotel Wi-Fi in Peru? Yeah, that’s a little suspicious. With Conditional Access, you can respond dynamically: maybe require another round of MFA, or block access entirely unless the device meets your compliance standards.
It’s also about balance. Security shouldn’t mean throwing users into a maze of prompts and roadblocks. When you do it right, Conditional Access helps you enforce the right level of protection without making people’s lives miserable. You can give your users a smooth experience—while making sure the sensitive stuff stays locked down tighter than a secret recipe in a vault.
And since Conditional Access works across your cloud apps, identity providers, and device states, it quickly becomes the backbone of your modern security strategy. This isn’t just a one-off tool—it’s how you start building a Zero Trust architecture, one smart policy at a time.
Core Components of Conditional Access
Okay, so before we go off crafting policies like mad scientists, let’s break down the building blocks that make Conditional Access tick. These are the core components that every policy touches in some way, and understanding them will save you a lot of frustration (and maybe a late-night help desk call or two).
1. Identity Signals – Who, What, Where, and With What
This is your first set of levers. Identity signals are all about who’s trying to do what:
- Users or groups – Is it a regular user? A guest? A high-privilege admin?
- Devices – Are they on a corporate laptop, or some old Chromebook from a flea market?
- Locations – Are they signing in from a known corporate IP, or a coffee shop in another country?
- Applications – What service are they trying to access? Teams? SharePoint? Your HR system?
These signals are the raw ingredients. You’ll use them to shape your policy logic and decide what happens next.
2. Conditions – When and Why to Raise an Eyebrow
Conditions let you set the stage for action. Think of them as the “if” in your security “if-this-then-that.”
You can trigger policies based on things like:
- Platform – Windows, macOS, iOS, Android, etc.
- Sign-in risk – Is the sign-in marked suspicious by Identity Protection?
- Device compliance – Has the device passed all your Intune requirements?
- Client app type – Modern browser? Legacy protocol?
This is where you can get super specific—or keep it broad, depending on your comfort level and risk appetite.
3. Controls – What You’re Actually Enforcing
Once you’ve scoped out the who, where, and what, it’s time to lay down the law.
This is where you define what needs to happen before access is granted:
- Grant controls – Require MFA, allow only compliant devices, enforce password reset, etc.
- Block controls – Just say “nope” entirely if the scenario is too risky.
- Session controls – Fine-tune how long sessions last, control persistence, or even trap users in a browser-only session using Defender for Cloud Apps.
Session controls, in particular, are magic for keeping access locked down even after the front door is opened.
Heads-up: You’ll need the right licensing for Conditional Access—something like Microsoft Entra P1 or P2, or part of an E3/E5 bundle. Without it, you’re going to hit some walls real fast.
Setting Up Conditional Access Policies
So, now that you know what Conditional Access is and why it’s awesome, let’s actually build something.
We’re going to walk through setting up a policy that requires all users to go through multifactor authentication (MFA). This is Security 101—and trust me, if you haven’t done this yet, your tenant is basically wearing a “Kick Me” sign on its digital back.
Important PSA: Microsoft now requires MFA for all admin portal access, which started in 2024. So, if you’re thinking, “Maybe I’ll do this later,”—you’re already behind.
We’re going to build this from scratch so you can see the whole process. Yes, there are templates, but understanding the steps gives you way more control down the line.
Step-by-Step: Requiring MFA for All Users
- Head to the Entra Admin Center or Azure Portal
Either works—just depends on your flavor of choice. - Open Conditional Access
- In Azure: Search for “Conditional Access” and open “Microsoft Entra Conditional Access.”
- In Entra Admin Center: Go to Protection > Conditional Access.
(Pro tip: Hit the star icon to favorite it for quicker access next time.)
- Click “Policies” at the top left.
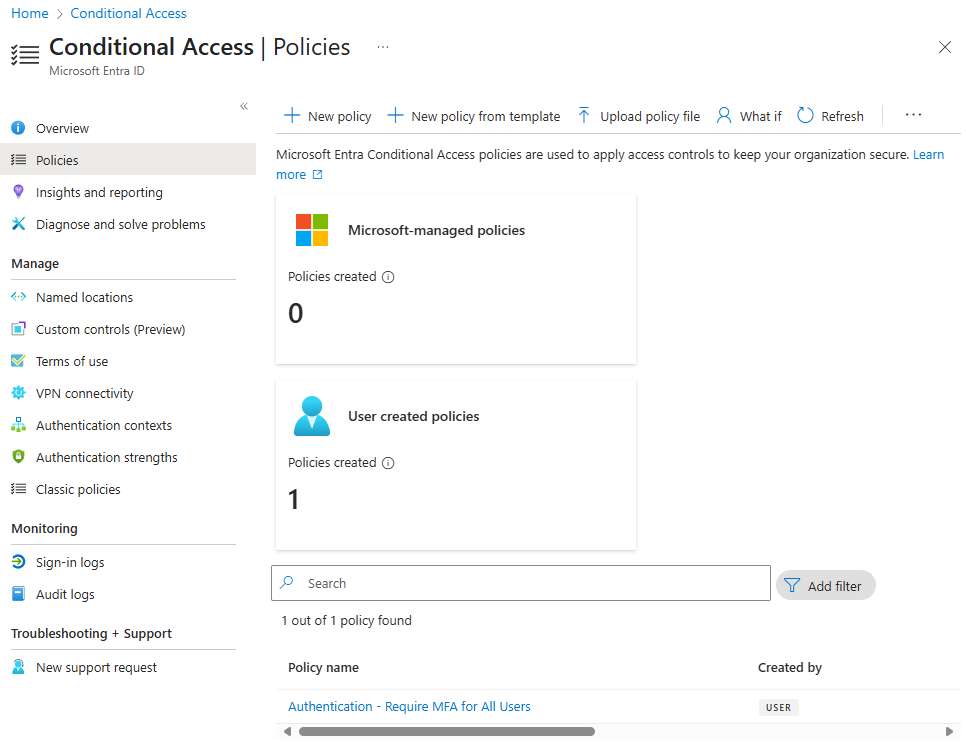
- Hit “New policy”
Sure, there’s a template called “Require MFA for all users”, but we’re doing this manually so you understand how everything fits together. - Name your policy
Something like Authentication – Require MFA for All Users works. Naming conventions are your friend—especially when you have dozens of policies and need to troubleshoot in a hurry.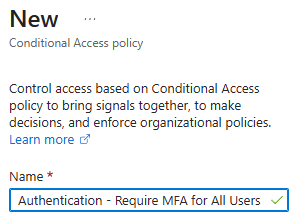
- Target your users
Click the blue Users link and select All users.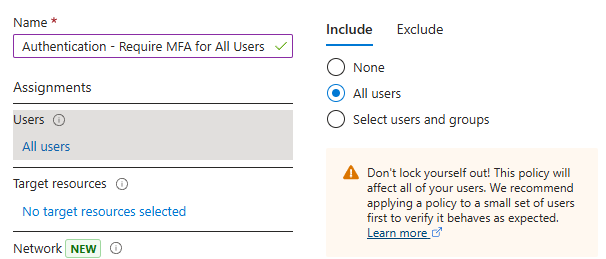
STOP! Exclude your break-glass or emergency accounts.
These should be highly privileged accounts with long passwords and no Conditional Access restrictions—just in case you accidentally lock everyone out (yes, it happens… and yes, it’s awkward).
- Target cloud apps/resources
For this demo, we’re protecting access to everything, so select All cloud apps.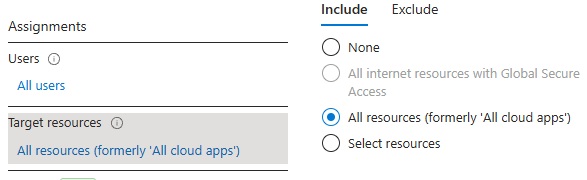
- Skip network conditions for now
We’re not filtering by IP or geography today—but just know you can get very specific here later. - Set Conditions → Client Apps
Focus on modern authentication clients—browsers, mobile apps, desktop clients.
We’re skipping legacy clients for now (but hint: your next policy should block legacy authentication—there’s a template for that!).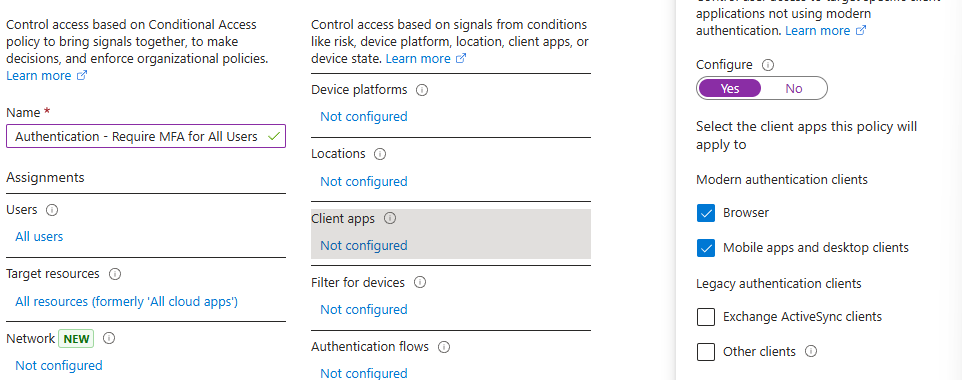
- Grant Access with Authentication Strengths
- Under Grant, select Require authentication strength.
- Pick Passwordless MFA if you want to ditch SMS and go with stronger options like FIDO keys or phone sign-in.
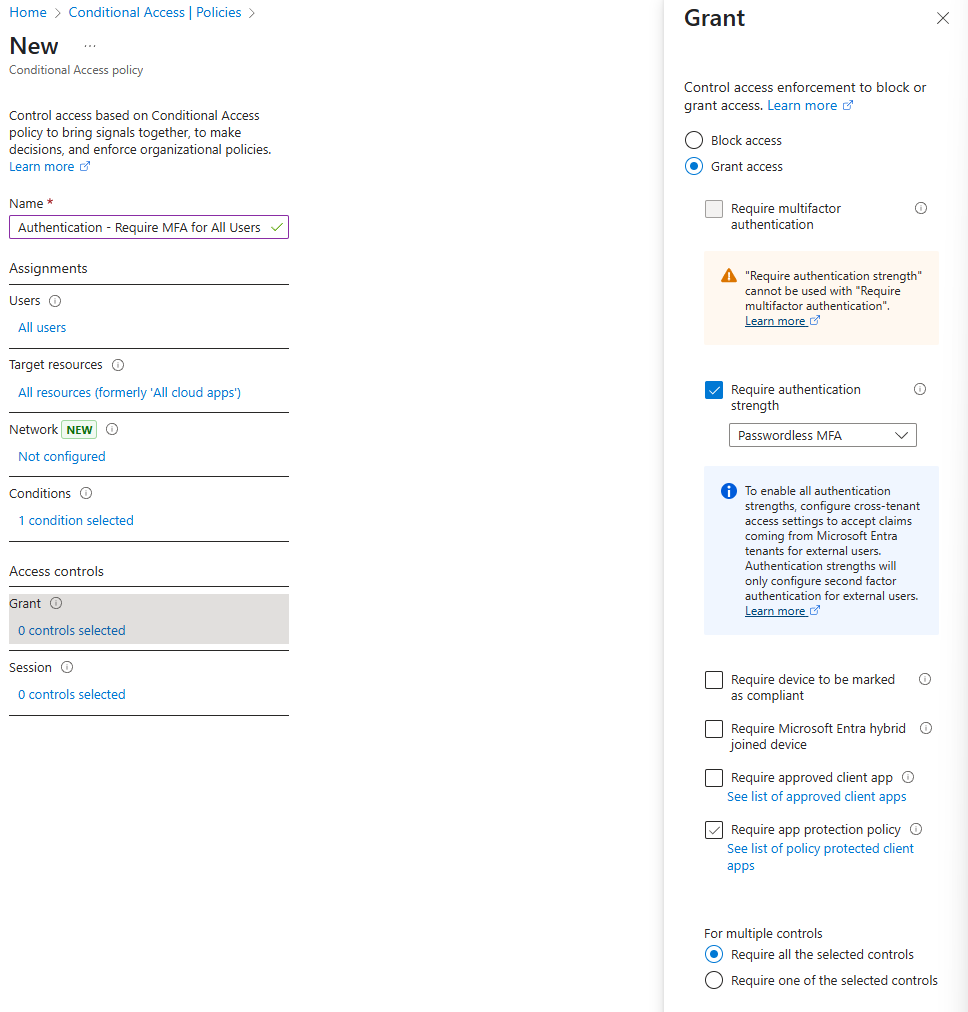
You can customize your authentication strengths to fine-tune what counts as “strong enough.”
- Leave “Require all selected controls” checked
In this case, we’re only asking for one thing: the authentication strength. - Set the policy to “Report-only” mode
This is huge. Always start in report-only. It lets you test the waters without locking out the entire company (or yourself). - Click “Create”
You’ve just created your first custom Conditional Access policy!
Verifying the Policy
Once it’s live (well, “reporting”), go to the Sign-in logs under Entra. Look at user sign-ins, and you’ll see which Conditional Access policies were applied—or skipped. This gives you a real-world preview of how things will behave.
When you’ve tested thoroughly, go back to the policy and flip the switch from Report-only to On.
Congrats, you’re officially enforcing MFA.
Next Step: Block Legacy Authentication
Modern authentication is great—but if you leave legacy auth enabled, attackers will find the back door.
- Go to Policies > New policy from template
- Pick “Block legacy authentication”
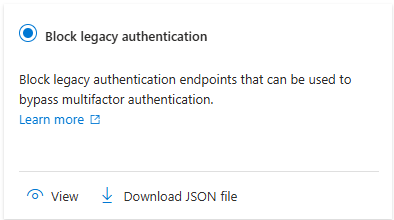
- Click Review + Create
- Rename the policy to something useful (e.g., Block Legacy Auth – All Users)
- Set it to On
- Hit Create
Boom. Two foundational policies in place.
Big Note: Always test policies with a pilot group. You’ll thank yourself later. It’s far too easy to click the wrong box and shut out half your org—or yourself. Conditional Access is powerful, but it’s not forgiving if misconfigured.
One more thing: If you’re creating a Conditional Access policy for a specific group—like Finance folks accessing a sensitive SharePoint site—don’t forget to handle the other side of that scenario.
Here’s what happens if you don’t: Finance gets hit with all the right restrictions (MFA, compliant devices, etc.), but everyone else? They stroll right past the bouncer because no one told them they couldn’t enter.
So, what do you do? Create a second policy for “everyone else” that either blocks access or adds the right guardrails—and then exclude your original Finance group from that second policy. It’s all about covering both sides of the access coin.
Beyond Conditional Access
Alright, now you’ve got the basics of Conditional Access down. But this is just the beginning—like building the foundation of a house and thinking you’re done. Conditional Access is a critical layer, but what really makes it shine is how it integrates with other Microsoft tools. Let’s talk about some of those integrations that can take your security to the next level.
Microsoft Defender for Cloud Apps: The Cloud App Security Broker
If you haven’t heard of Defender for Cloud Apps (formerly known as Microsoft Cloud App Security), it’s part of the larger Defender XDR suite and your best friend when it comes to cloud app security. Essentially, it’s the Cloud App Security Broker (CASB) that ties into your Conditional Access policies and extends them even further.
Why does this matter?
Let’s say you have a policy that allows users to access your SharePoint site—but they’re logging in from a non-compliant or personal device. Defender for Cloud Apps can step in and put them into a “session” where they can only view documents but can’t download, print, or copy/paste the contents. The security doesn’t stop once the user gets in—it continues throughout the session.
This gives you another layer of control to manage how users interact with your data once they’re inside your environment. It’s one thing to block entry; it’s another to control what happens once they’re in.
Identity Protection: Automating Remediation for Risky Users
Now, let’s talk about Identity Protection. When you hook up Conditional Access to User Risk and Risky Sign-ins/Users, it can automatically trigger remediations for users showing signs of being compromised. Think of it as a virtual bodyguard that jumps into action the moment something’s off.
Real-World Example:
If someone logs in from a suspicious location—or their account is flagged as compromised—Conditional Access can require a password reset, or a series of extra MFA steps. It’s like sending a user through a digital metal detector every time they try to log in.
This integration automates a huge part of security, ensuring you don’t need to manually monitor or respond to every little security risk. Instead, let the system flag the problems and handle them automatically—so you can focus on bigger issues.
Role-Based Access Control (RBAC) and Zero Trust: Layering Security for Maximum Control
Conditional Access doesn’t just work in a vacuum. It’s part of a broader strategy for implementing Zero Trust and Role-Based Access Control (RBAC). By layering these tools together, you’re able to assign roles and permissions based on who a user is, what they’re trying to access, and where they’re logging in from.
Think of it like this:
With RBAC, you’re assigning roles to users—like admin, manager, or employee. With Conditional Access, you’re adding a second layer that controls what happens when those users access resources. A simple example: a user might have a “Manager” role, but they can’t access financial data unless they’re logging in from a compliant device. It’s all about making sure users only get access to what they need, and nothing more.
With RBAC, you’re defining access levels. With Conditional Access, you’re defining access conditions—whether they’re logging in from a trusted location, using compliant devices, or having passed through MFA.
Wrapping It Up
At this point, you’ve got the tools and the knowledge to secure your Azure environment with Conditional Access. But remember, Conditional Access is just one piece of the puzzle. The true magic happens when you start layering it with other tools like Defender for Cloud Apps, Identity Protection, and RBAC.
These integrations help ensure that the right users, using the right devices, are accessing the right resources—and nothing more. By using Conditional Access alongside these tools, you’re creating a comprehensive security strategy that can adapt and evolve as your needs grow.
Now that you’ve got Conditional Access and these integrations covered, you’re ready for the next stage. Keep tuning your policies, get familiar with the advanced settings, and always be testing—because security doesn’t stay static. Neither should you.
Headin’ Out
And there you have it—Conditional Access in all its glory! From setting up basic policies like MFA for your entire tenant, to integrating with other Microsoft security tools like Defender for Cloud Apps and Identity Protection, you’re on your way to building a robust security framework that doesn’t just work, but works smartly.
Remember, Conditional Access is your security foundation, but it’s the integrations with other tools that will really let you fine-tune access control and security policies to fit your organization’s unique needs. The best part? It’s flexible. Whether you’re keeping things simple with MFA or diving deep into role-based access control, the power is in your hands to balance security with productivity.
Takeaways:
- Start simple, test often: When rolling out new Conditional Access policies, start with a “report-only” mode and test with small groups before going wide.
- Think layers, not silos: Conditional Access isn’t a one-and-done deal. Integrate it with tools like Defender for Cloud Apps and Identity Protection to lock down your security in layers.
- Security doesn’t stop at the door: Once someone’s inside, keep controlling what they can do with the data via session controls and app-specific restrictions.
By implementing the right policies and integrations, you’ll keep your Azure environment secure without getting in the way of productivity. And as with all things security, it’s a journey. As your organization grows and evolves, so too will your security policies and strategies.
So, don’t rest just yet. The next step is to dive deeper into the advanced features of Conditional Access, integrate even more Microsoft tools, and keep an eye on user behavior and security risks. Because in the world of cloud security, staying ahead of threats is a marathon, not a sprint.
Thanks for joining me on this deep dive into Conditional Access. I hope you found this guide useful, and I look forward to sharing more on how you can lock down your cloud environment and make it as safe as possible in the days ahead!

Leave a comment